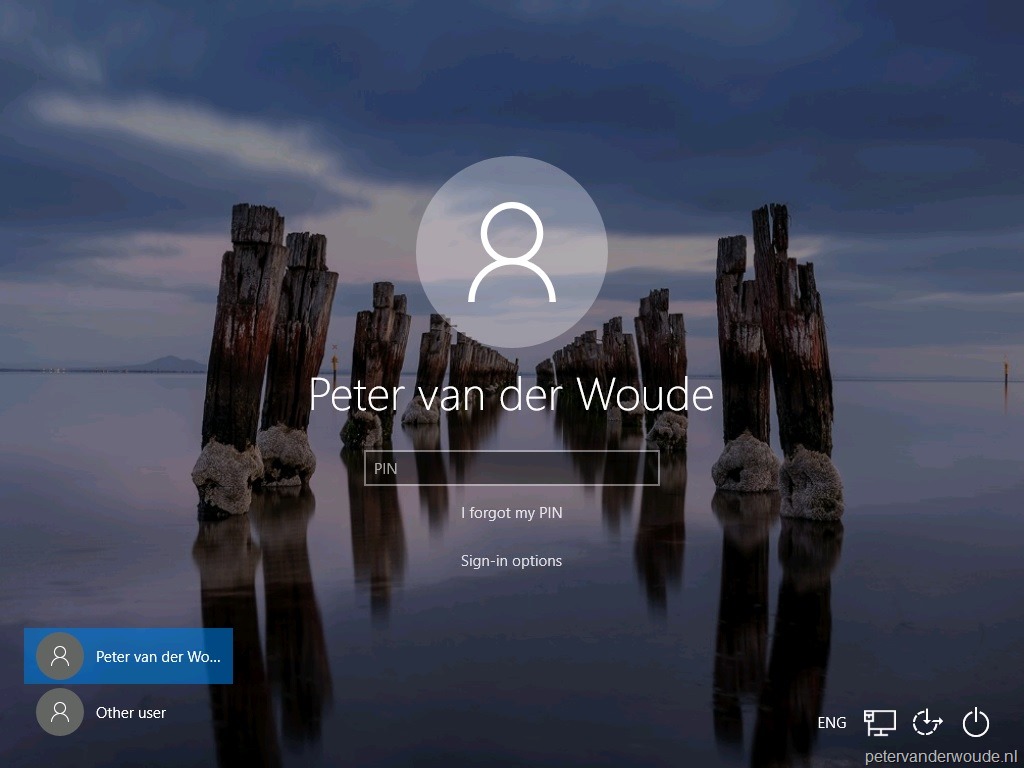
Logging into your computer can be a repetitive task, if you use multiple accounts or have strong, complex passwords. LogonExpert provides a seamless solution by automating the login process, saving you time and effort. With its efficient and reliable system, users can enjoy a hassle-free start to their computing experience. By downloading LogonExpert, you gain access to a tool designed to enhance productivity while maintaining security. The software ensures that your system logs in automatically, letting you focus on important tasks without worrying about entering credentials repeatedly.
Effortless Automatic Login
LogonExpert download simplifies the process of accessing your computer by storing your login information securely. Once set up, it automatically logs you in every time you start your system. This feature is particularly useful for professionals who need quick access to their desktops and for home users who want a smoother computing experience. Key benefits include:
- Eliminates the need to type passwords repeatedly
- Reduces login time to seconds
- Supports multiple user accounts
- Compatible with Windows operating systems
Quick and Easy Setup
Setting up LogonExpert is straightforward and requires minimal technical knowledge. The installation process is user-friendly, guiding you through each step to configure automatic login securely. Within minutes, your system can be ready for automatic access, ensuring convenience from day one.
- Simple installation wizard
- Step-by-step guidance for configuration
- No advanced skills required
Secure and Reliable
Security is a top priority when automating logins. LogonExpert ensures that your credentials are encrypted and stored safely on your system. The software operates locally, reducing the risk of online threats while maintaining full access to your accounts. Reliability is another key aspect, as LogonExpert works consistently without affecting system performance.
- Encrypted credential storage
- Local operation for enhanced security
- High reliability without system slowdowns
Boost Productivity
Automatic login allows users to start working immediately, which can enhance productivity in both professional and personal environments. By eliminating the repeated task of entering passwords, LogonExpert saves time and streamlines your workflow. It also supports users with multiple accounts, making it easy to switch between profiles without hassle.
- Immediate access to your desktop
- Supports multi-account setups
- Saves valuable time every day
Downloading LogonExpert offers a convenient and secure way to experience automatic logins. With easy setup, strong security measures, and reliable performance, it ensures users can access their computers without delay. By automating the login process, LogonExpert transforms daily routines into smoother, more efficient experiences. Users benefit from time savings, simplified access, and consistent system performance, making it a practical tool for anyone seeking efficiency and convenience in their daily computing activities.






